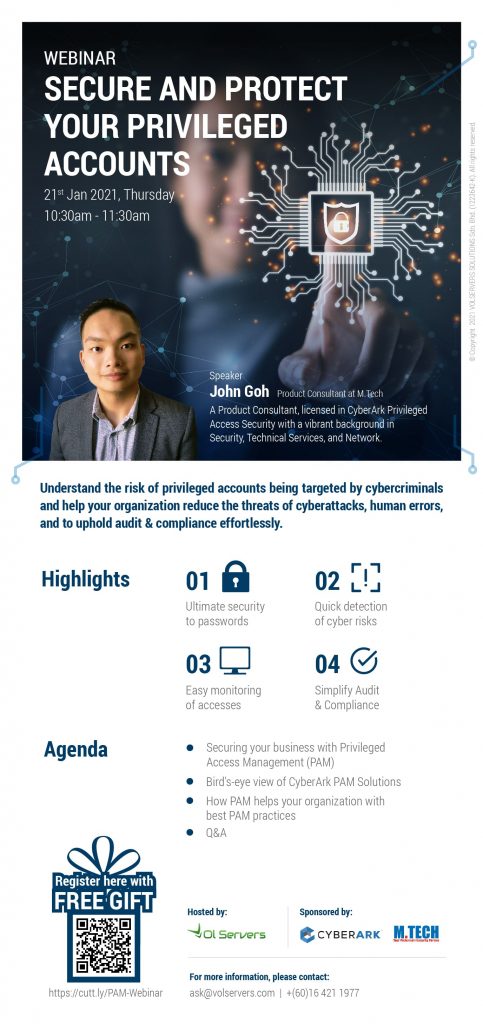
Volservers Solutions has hosted a webinar regarding ‘Privileged Access Management’, sponsored by CyberArk & M.Tech Pro Malaysia on 21st January 2021. The webinar is successfully held with more than 20 attendees from different industry in Malaysia.
Some Questions Asked during the Webinar
1. Is Privileged Access Management (PAM) a step up from Identity Access Management (IAM)?
Privileged Access Management (PAM) and Identity Access Management (IAM) differ between one another. Privileged Access Management (PAM) protects users with privileged access to sensitive data, Identity Access Management (IAM) deals with a business’s everyday users. Due to this difference in audience, the data breach surface being addressed by Privileged Access Management (PAM) and Identity Access Management (IAM) differ. Privileged Access Management (PAM) protects access to business and technical functions, whilst Identity Access Management (IAM) protects against a low number of business-specific applications. Given privileged users’ critical attack surface, a Privileged Access Management (PAM) solution should always be primarily implemented, followed by a complimentary Identity Access Management (IAM) solution.
2. What are the advantages of AZURE AD?
Azure Active Directory (Azure AD) is Microsoft’s enterprise cloud-based Identity and Access Management (IAM) solution. Azure AD is the backbone of the organization subscribing to Microsoft’s Office 365 system. It can sync with on-premise Active Directory and provide authentication to other cloud-based systems via OAuth.
3. Can I run a DNA tool myself to find and understand available privilege accesses in my environment?
You may engage Volservers for more Digital DNA data evaluation and ensuring of security measures.
What is Privileged Access?
Privileged access is an administrative or super-user access that allows for the full control of critical computer systems and applications anywhere, and at any time. It is a set of policies, processes and tools that protect, manage, and monitor privileged access, users, and credentials.
Why you need Privileged Access Management?
- Ultimate Security to Passwords
- Quick Detection of Cyber Risk
- Easy Monitoring of Accesses
- Simplify Audit & Compliance